The No-Code Gap: What Most AI Agencies Don't Know They're Selling You

Most AI agencies in Spain and the EU sell Zapier and Make for problems those tools were never built to solve. Where they belong, where they break, what to ask before signing.
A logistics SME in the Madrid corridor showed us the demo their AI agency had pitched. Five apps wired together in Zapier, a Make scenario routing customer data between two SaaS, all built in under an hour. It looked clean.
Then we asked what happens when an order arrives during a token refresh, when the GDPR data passes through US infrastructure, when a webhook returns 200 but the downstream system never gets the event. The agency had no answer. The product worked in the demo. It would not survive contact with a regulated EU production environment.
This is the no-code gap. It is the distance between what these tools genuinely do well and what a growing slice of the AI agency market sells them as solving. The gap is not theoretical: 42% of European and North American organisations abandoned most of their AI initiatives in 2025, up from 17% the year before (S&P Global / 451 Research, Oct 2025, n=1,006). Most of those projects did not fail because the technology was wrong. They failed because the scope did.
For the data on which tasks AI actually automates reliably, see What AI Actually Automates in 2026. For the role-by-role view, see Which Roles AI Is Really Changing.
Key takeaways
- 42% of organisations abandoned most of their AI initiatives in 2025, up from 17% in 2024; the average org scrapped 46% of POCs before production (S&P Global / 451 Research, Oct 2025).
- OWASP’s Low-Code/No-Code Top 10 lists account impersonation, authorisation misuse and silent data leakage as the dominant risks, most of them triggered unintentionally by non-technical builders (OWASP, 2024).
- Webhook delivery success drops to 94.2% during EU peak hours, with 3.8% of failures returning HTTP 200; in plain language, the workflow says “ok” while the event is lost (Carrier Integrations, 2025).
- No-code tools are right for narrow, recoverable, non-regulated workflows. They are wrong for most of what European agencies are currently selling them as solving.
The market is growing. So is the failure rate.
The low-code/no-code market is valued at $37.4 billion in 2025 and projected to reach $376.9 billion by 2034, a 29% CAGR (Fortune Business Insights, 2025). Investment is accelerating. Production results are not. S&P Global’s October 2025 survey of 1,006 mid- and senior-level IT professionals across North America and Europe found project abandonment nearly tripled in twelve months.
These two curves describe the same moment. Money is flowing in. POCs that should never have left the slide deck are being built, deployed, and quietly killed.
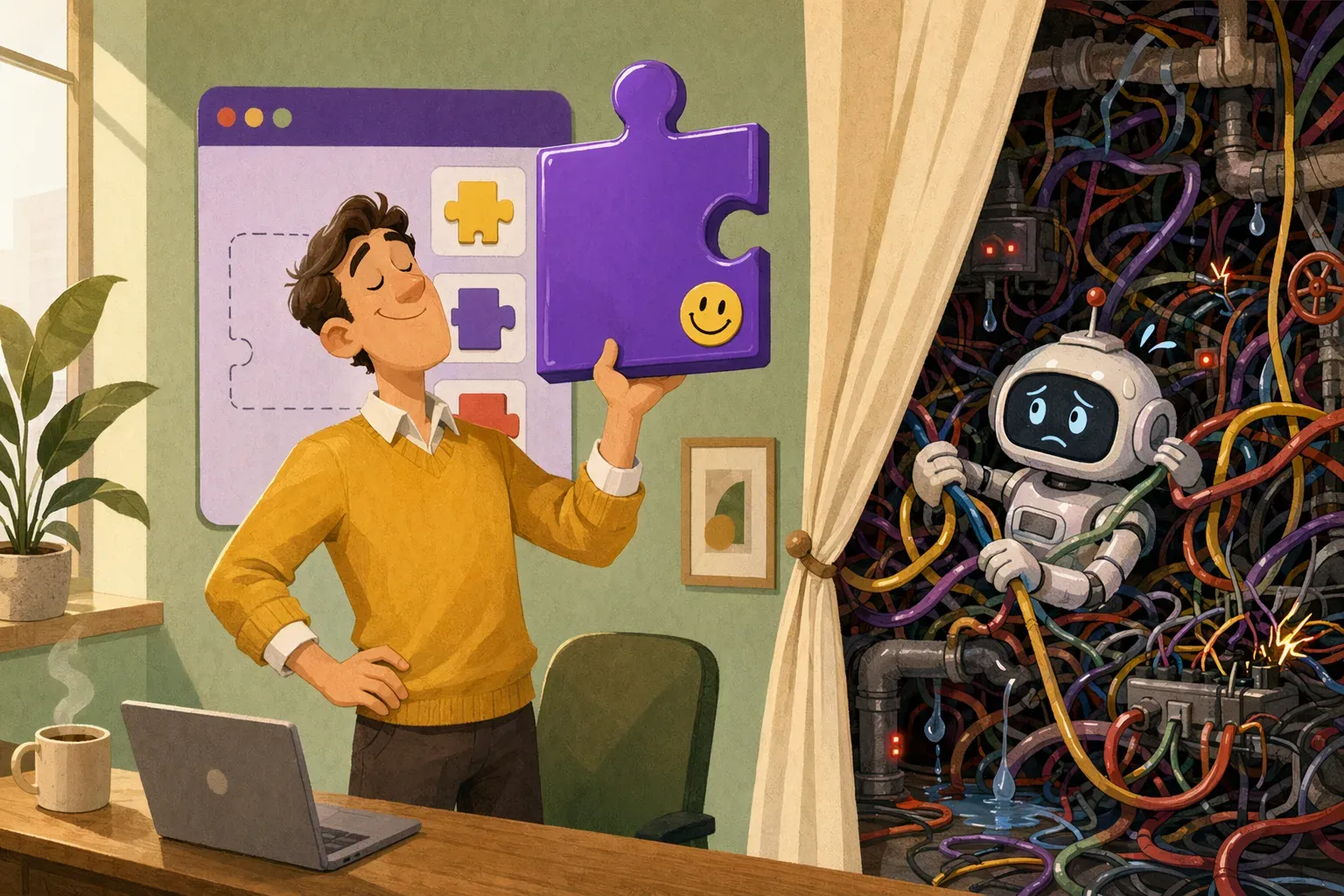
The pattern is consistent: projects scoped for the demo, not for production. The integration complexity, error handling, monitoring and compliance overhead surface only after rollout, when the agency has already invoiced the build.
No-code automation tools — Zapier, Make (formerly Integromat), n8n — are useful inside a defined scope. The problem is not the tools. The problem is what agencies sell them as.
Where no-code tools actually belong
No-code tools are not bad. They are bounded.
The honest scope is narrower than the marketing suggests: simple linear trigger-action flows, low data sensitivity, well-supported apps via official connectors, internal use cases where a failure is recoverable, and teams where non-technical staff need to edit the automation themselves. A Zapier flow that pings Slack when a row appears in a Google Sheet is a sensible use of a sensible tool. A Make scenario syncing contacts between two CRMs with standard field mapping holds up under those conditions.
Gartner forecasts that 70% of new applications will use low-code or no-code tooling by 2025 (Gartner via KissFlow, 2024). That figure reflects real utility. Not everything needs custom engineering.
Where the boundary breaks. Any of these conditions changes the architecture you need:
- The data is personal data regulated under the GDPR, the LOPDGDD or the EU AI Act high-risk categories.
- The integration requires non-standard authentication: mutual TLS, IP allowlisting with dynamic ranges, custom token refresh logic.
- The workflow has more than three conditional branches or needs to retain state between steps.
- The process is revenue-critical and an unrecoverable failure is unacceptable.
- The business operates in a regulated sector: banking, insurance, healthcare, public administration.
Cross any of those lines and the design assumptions baked into no-code tools start working against you. Most agencies do not surface this before the contract is signed.
The technical limits no demo shows you
What does “breaking at the integration layer” look like in production? Four failure modes show up again and again.
Custom authentication
Zapier and Make support a fixed catalogue of auth patterns: standard OAuth 2.0, API keys, basic auth. When a Spanish bank or a SaaS vendor uses non-standard token refresh, mTLS or IP allowlisting that rotates by region, the connector either fails or asks the builder to put credentials somewhere they should not live. Agencies rarely raise this in the demo because the demo uses a fully supported app.
Stateful workflows
No-code tools model work as stateless trigger-action chains. A process that has to wait for a human approval, retry on a timeout, or pick up where it left off after a partial failure either gets a brittle workaround built on an external database, or needs a system designed for state from the start. Agentic workflows fall in this second bucket. They are not Zapier flows with extra steps.
Error recovery
What happens when step 4 of a 7-step flow fails at 02:00 on a Saturday? In a custom integration designed for production, the error is caught, logged with full context, retried with backoff and surfaced to an alert channel that wakes someone up. In a Make scenario, by default, the scenario stops and an email may or may not arrive depending on notification settings.
Silent failures
This is the one no agency ever brings up unprompted. Webhook delivery success drops to 94.2% during EU peak hours (09:00–11:00 CET), and 3.8% of those failures return HTTP 200: the receiving system reports success while the event never triggers downstream processing (Carrier Integrations, 2025). Average weekly API downtime climbed from 34 minutes in Q1 2024 to 55 minutes in Q1 2025 (UMA Technology, 2025).
In a flow processing 500 events a day, a 3.8% silent failure rate means roughly 19 lost events every day. Nobody notices until a customer calls, a payment goes missing, or a regulator asks for a report nobody can reconstruct.
The no-code tool logged “success.” The business experienced failure. — pattern observed in three audits we ran for EU SMEs in 2025
The compliance blind spot in Spain and the EU
For any business operating under the GDPR, the EU AI Act or sector-specific regulators, no-code tools carry a structural risk that is not a configuration problem. It is an architectural one.
European data protection authorities recorded over 400 personal data breach notifications per day between late January 2025 and January 2026, a 22% year-on-year increase, with GDPR fines around €1.2 billion in 2025 (Feroot Security, 2025–2026). A meaningful share of those incidents trace back to misconfigured third-party integrations.
Two issues that almost never make it into a no-code agency’s proposal:
Where the data physically goes. Zapier routes all workflow data through AWS infrastructure in the United States. Make’s processing servers are EU-based, but the platform’s sub-processor list and data processing agreements add compliance surface area that few Spanish or EU agencies actually audit before recommending the tool. For HIPAA-equivalent scenarios in Spain — clinical data under the LOPDGDD, banking data under DORA and Banco de España requirements, insurance data supervised by the DGSFP — the relevant question is not “is there a DPA?” but “is the entire processing chain admissible under our regulator’s current criteria?”
Who carries the liability when things break. OWASP’s 2024 Low-Code/No-Code Top 10 names account impersonation, authorisation misuse, data leakage and security misconfiguration as primary risk categories. The framework explicitly notes that citizen developers — non-technical staff using these tools the way they are designed to be used — trigger many of these vulnerabilities by accident (OWASP, 2024). One documented incident: a single low-code deployment with a “Table Permissions” privacy setting off by default exposed 120,000+ files and 1.7 million activity logs anonymously (OWASP / DEV Community, 2024).

There is also a Spanish operational layer most US-headquartered agencies miss entirely. Any automation that affects how staff work — how leads are routed, how shifts are assigned, how sales productivity is measured — sits inside the Estatuto de los Trabajadores and, in larger employers, inside the works council’s right to information. Building that without consulting the comité de empresa is not a compliance footnote. It is grounds for the deployment to be paused.
What “right for specific scopes” actually means
The argument is not that no-code should never be used. The argument is that its appropriate scope is narrower than most agency proposals describe, and that the criteria are concrete.
Before any no-code tool is proposed, every one of these has to hold:
- The data is not personal under the GDPR or sector-regulated.
- The workflow is linear; branching is shallow and exception handling is recoverable.
- The integrations use natively supported connectors with standard auth.
- A failure is non-critical and reversible.
- The vendor’s current API uptime profile is acceptable for your SLA.
If any condition fails, you do not need a more complex Make scenario. You need a different architecture.

Alpha Software’s research found that 39% of business leaders cite limited customisation as a significant no-code challenge, and the same share say no-code is unsuitable for advanced problems (Alpha Software, 2024–2025). “Unsuitable” is the charitable framing once patient data, financial records or works-council-relevant flows enter scope.
Questions to ask any agency before signing
The gap between what an agency claims and what no-code tools deliver normally stays invisible until the project is mid-flight. These questions surface it earlier.
On tool selection
- Which specific tools are you proposing, and why are they appropriate for this workflow’s data sensitivity and failure tolerance?
- Are the connectors native or custom-built? What happens when the underlying API changes?
On compliance
- Which infrastructure does data physically pass through, in which country?
- Have you reviewed the DPA and sub-processor list of each tool against our GDPR and sector requirements?
- For regulated data (banking, health, insurance, public sector), what is your approach to the LOPDGDD, DORA or DGSFP framing at the integration layer?
- If the deployment changes how staff work, how do you plan to inform the comité de empresa?
On reliability
- How does the automation behave if step 3 of a 7-step flow fails?
- How will we know when events are silently dropped? What monitoring sits on top of the platform?
- What is the on-call protocol when this breaks at 02:00 on a Saturday?
On engineering depth
- What is the most complex custom integration your team has built without a no-code tool?
- Do you write code? When the workflow outgrows what Make can handle, what is your migration path?
An agency that cannot answer these with specifics has not thought past the demo. That is not the agency you want managing flows that touch your customers, your payroll, or your regulated data.
The diagnostic question is not “should we automate?” It is “does this specific workflow meet the conditions where automation generates durable return — at the integration layer, under real load, with the data sensitivity we actually have?”
Diagnose which tasks in your team can actually be automated — free at canihireanai.com.
Frequently asked questions
Is Zapier safe for business use in Spain or the EU?
Zapier is a sensible tool for simple, low-stakes flows with low data sensitivity and linear trigger-action logic. It becomes a liability when handling GDPR or LOPDGDD-regulated data, when custom auth is required, or when revenue-critical processes run without fallback logic. The tool is not the risk. The scope mismatch is (OWASP, 2024).
What is n8n and how does it differ from Zapier?
n8n is an open-source workflow automation tool that reached 230,000+ active users and $40M ARR by late 2025, raising $180M at a $2.5B valuation (Sacra, 2025). It is more flexible than Zapier — self-hosting, custom code nodes, deeper branching — but it shares the same architectural limits for stateful workflows, complex error recovery and regulated data.
Why do AI automation projects fail so often?
S&P Global’s 2025 survey found 42% of organisations abandoned most AI initiatives, up from 17% in 2024, with the average org scrapping 46% of POCs before production (S&P Global / 451 Research, Oct 2025). The most consistent root cause: scope built for the demo, not for production. Integration complexity and missing error handling only emerge after rollout.
How do I tell if an agency is over-relying on no-code tools?
Ask whether they write code. Ask how they handle runtime failures. Ask specifically about compliance at the integration layer and works-council implications. Agencies over-relying on no-code typically answer with vendor documentation rather than their own engineering practices.
The gap nobody advertises
No-code tools exist because a lot of useful automation genuinely does not need custom engineering. That is not changing. n8n’s $180M round at a $2.5B valuation reflects real demand, not a bubble.
The problem is narrower. A growing slice of the AI agency market in Spain and the EU has built its business model on selling no-code as a comprehensive solution. The staff knows how to configure Make scenarios. They do not know how to design an event-driven architecture, write a custom webhook handler, scope a data processing agreement under DORA, or draft an EU AI Act conformity assessment.
They do not know what they do not know. By the time the buyer discovers it, the contract is already signed.